When cloud computing was first introduced to the consumer market, the technology required a fair amount of explaining. Today, the cloud is widely utilized by consumers, despite the fact that 51 percent of the public believe that actual clouds are somehow involved. Due to so many people using the cloud, consumers are now approaching computing much differently.
When cloud computing was first introduced to the consumer market, the technology required a fair amount of explaining. Today, the cloud is widely utilized by consumers, despite the fact that 51 percent of the public believe that actual clouds are somehow involved. Due to so many people using the cloud, consumers are now approaching computing much differently.
Even though most consumers may not know exactly how the cloud works, they have changed their expectations about computing because of their exposure to it. Namely, consumers expect whatever cloud service they use to be reliable and accessible. When it comes down to it, these expectations about the cloud actually trump all other expectations for computing technology.
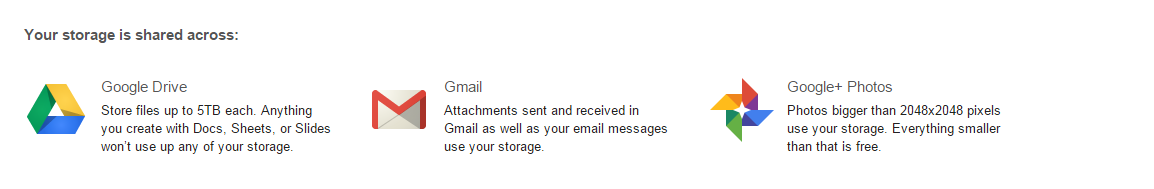
Think about it, there was a time when consumers put a lot of stock into getting the most powerful home PC they could afford. Today, the average consumer has multiple devices of varying quality, spread out between their home and office. Thanks to the cloud, users are able to access their needed files on each one of these devices, meaning that the specs of the hardware take a backseat to the reliability of the device’s cloud software.
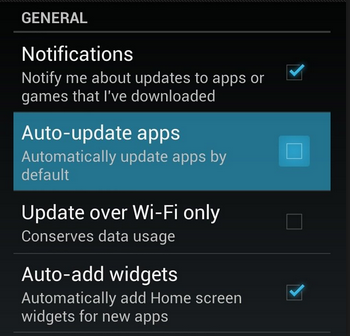
Additionally, the development of cloud services has gone in the direction of making the technology ultra-convenient for consumers to use. This too has influenced the expectations that consumers have regarding their cloud software, making it so that users expect installs, upgrades, and issues be resolved with just a few clicks. This is quite a leap from the days of purchasing software on CD-ROM and transporting files via USB thumb drive.
One tech blogger who does a good job articulating the high demands of today’s consumers is ZDNet’s David Gewirtz. Speaking on behalf of the consumer, Gewirtz compiles an accurate list of what today’s consumer looks for in a cloud service offering:
- Some cloud services are free, but we expect premium upgrades.
- If paid services are involved, we expect to easily and smoothly add or remove services merely with a mouse-click and a credit card.
- As soon as a service plan’s capacity is reached (or just before), we expect the service to offer us an upgrade, not require us to go hunting to make things work.
- We also expect fees to be tiered, so that each new tier provides more value than the last, with an incremental fee or jump.
- Fees are usually all-you-can-eat for a year or smoothly scalable as soon as more capacity is needed.
- We expect to be able to use the service on any compatible machine.
- And we generally expect the service to work on pretty much anything.
- We expect all our service-related data to just be there, wherever we are. How that happens is not our problem.
- Installation is a click or a login. That’s it. It’s just there. There are no longer installers, updaters, zip files or other things to download and run on the desktop. Just click and run.
Does your company’s current cloud solution meet these expectations? If it doesn’t, then there is likely another cloud solution available that does. NuTech Services can provide you with the cloud services your business needs to succeed. In the same way that the cloud has completely improved utility computing, we feel like revolutionizing your IT infrastructure is a reasonable expectation to ask of your IT company. Call us at 810.230.9455 to learn more.




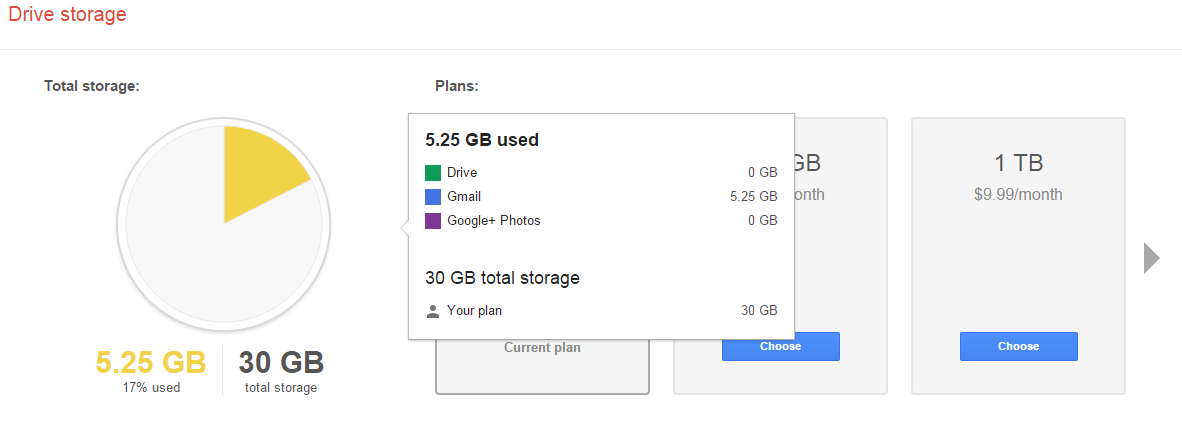
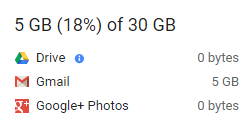



















 Monitor Your Current Data Usage
Monitor Your Current Data Usage