Not that long ago, the trading floor of the New York Stock Exchange was filled with business-tie clad gladiators, climbing over each other in what looked like a capitalism-induced mosh pit. The Open outcry pit had its language, its own weather, its own smell. Nowadays, these pits are more subdued. They still are populated with people, and some are gesturing to buy and sell, but most of the transactions are done digitally. It is this role where the computer has changed the way financial markets work; from the ground up.
The Street Before the Internet
The first thing you should know is that computation of some sort has been utilized by traders and brokers for decades. With that truth out of the way, today’s Wall Street doesn’t resemble the Wall Street of old at all. Long gone are the days where traders would make trades out the window, stand in the street during a snowstorm to buy and sell securities, and even later, sit in their offices and read stock prices off a ticker tape, or later, a teleregister (or quotation board).
These technologies all supercede the technologies of today, and go a long way toward paving the way for the instantaneous trading you see in hedge funds and brokerage houses today. In fact, once the personal ticker was invented during the second half of the twentieth century, and traders could get nearly instantaneous updates at their home or office, the stage was set for dynamic investor growth. In the 1980s the Quotron used more modern computing tactics to produce the same effect: providing individuals with up-to-the-minute trading information. These technologies, while all cutting-edge for their times, don’t have the enormous effect that today’s technologies have for investors.
The Street and the Internet
In order to monetize, commercialize, and totally legitimize the new Internet, there first needed to be capital in place to build the necessary infrastructure required in order to process and send all the data that people send via the Internet. Many people take this infrastructure for granted today, but there was a time, in the infancy of the Internet where Wall Street was trying to get a hold on all of the available new technologies. After all, brokerages had been using something called Electronic Communications Networks (ECNs) to create efficiencies for brokerages since the early 1970s. Like most of western society, brokers were wholly unprepared for the speed in which these new networking technologies would change the market.
The big shift began in 1994 when two economists, William Christie and Paul Schultz, published a paper titled, “Why do NASDAQ Market Makers Avoid Odd-Eighth Quotes?” where they outlined a deliberate anomaly where these market makers were manipulating the spread (the difference between the buy and sell prices of NASDAQ securities) to secure these individuals a higher profit margin. This led to a full scale investigation and, eventually, rule changes by the Security and Exchange Commission (SEC) to protect smaller investors. The demand fueled by more attractive (and fair) investment tools led to online brokerages such as ETrade and Ameritrade being created. These organizations offered flexibility to any individual investor and led to traditional brokerages, such as Charles Schwab and TD Waterhouse, moving much of their trading to the web.
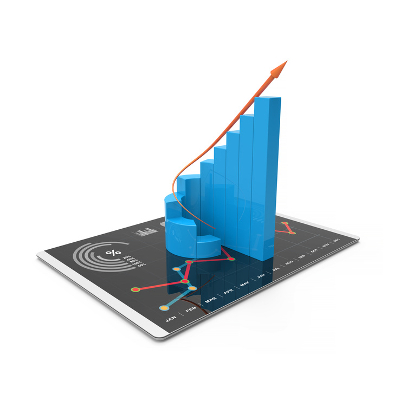
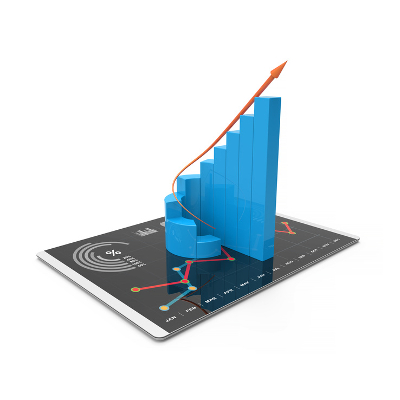
A few years later with more and more retail outlets popping up, Wall Street seemed to be in a spending frenzy over the next big Internet sensation. This led to what is known as the dot com bubble. Its explosion 1999 and 2000 paved the way for recession in many major western nations. As the economies in the EU and US rebounded, the improvement was largely driven by consumer and investor confidence that the Internet was here to stay, and that companies that had a viable business plan could find success by using the Internet as their sales base.
The Street at High Speed
After the housing market collapsed in 2008, the global economy hit the skids quickly. As a result, many of the strategies that were implemented to keep the world from sinking into a terrible depression were to add stimulus capital, without any real regulations about where the money was going to go. This has produced a wilder, less transparent, and overall fast stock market. With the use of today’s most dynamic Internet speeds, traders are now able to execute trades in incredibly short intervals; millions of times faster than the human mind can make a decision. Quantitative trading uses complex algorithms to do trades so fast that a half a cent here and a half a cent there can lead to millions of dollars changing hands over millions of trades.
This technology-driven trend is difficult for Wall Street regulators. Despite having state of the art solutions for monitoring these transactions, so many are made each day that it is practically impossible for people to keep their finger on the pulse of the market any longer. Regulators now rely heavily on automated systems that look for fraudulent activity in what seems to be a futile effort to keep investors, traders, brokers, and anyone else involved in this system, honest.
Nowadays, any major volatility of the market is largely the result of these micro-traders. Take the “Flash Crash” of May 6, 2010. The DOW, which had been losing ground all morning suddenly dropped 600 points, with Procter & Gamble losing 25 percent off its starting stock price. There was true frenzy on Wall Street, with the fear that we were looking into the abyss prevalent throughout the pundits and money managers all throughout the financial industry. In a matter of moments almost $1 trillion in shareholder value was erased.
The silver lining is that the market rebounded almost as fast as it fell and the DOW only finished down three points, but it took regulators over four months to determine what made the “Flash Crash” happen. It turned out that the problem stemmed from one of these algorithms being triggered by a very large sale of stock, along with the same-day announcement that Greece was bankrupt. When millions of trades can be made every minute, and are made every minute, there just isn’t the infrastructure there to provide entities the proper oversight the markets need to be thought of as “controlled”.
What do you think about the role of technology in the stock market? Do we need better oversight to ensure that fortunes are not lost in a blink of an eye, or that automation can’t take down the world economy? Or, do you believe that the market itself will dictate the end-game for technology in the financial sector?
To relate all of this back to your business, how has technology changed you? Has it made you faster, more automated, and more effective?
Leave your thoughts below in the comments.