Automation Can Remove Your Business’ Training Wheels

Automation as a concept is on the rise, and so too is its practice. Even before COVID-19 created considerable problems for several businesses, it was in use, and there is no reason for it to fall out of fashion now. There are plenty of ways your organization can implement automation to improve operations moving forward. […]
Tip of the Week: 3 Ways to Improve Your Business Technology’s Security

Businesses largely rely on their information systems and other technology tools, so you need to make sure they stay secure and far from the many threats out there. To this end, we recommend that you implement security systems that prioritize business continuity and data security. Let’s examine three ways you can keep your business’ IT […]
The Cloud Makes Critical IT More Affordable

Cloud technology has changed the way we do business, and it has provided countless opportunities for companies to achieve their wildest dreams. Granted, different businesses will use the cloud in different ways, but one fact remains the same: it makes financial sense to implement the cloud, no matter what type of business you are. Let’s […]
How to Prepare to Outlast a Data Disaster

When your business experiences a significant disruption, a disaster recovery plan is critical to getting back to normal. Some disasters are the result of external threats, while others come about from internal problems with your company’s operations. Here are some things you should consider when looking into potential disaster recovery solutions to help you get […]
A Digital Signage Revamp Can Change Your Business’ Optics

Have you ever considered why the VoIP auto attendant feature is so valuable? When a person is greeted with directions that make their journey easier, it typically improves their general opinion of your business. The VoIP auto attendant feature helps guide you through their telephone system. Now, have you ever been to a place where […]
Are Chrome’s Zero-Day Threats Actually a Good Thing?

With Google Chrome being one of the most popular web browsers out there, it’s no surprise that threats want to target it and take advantage of its users. However, up until recently, there have not been very many zero-day threats associated with Chrome. Zero-day threats are attacks that have never been seen before, affecting a […]
Businesses Should Consider Partnering with a Security Operations Center (SOC)

Cybersecurity is incredibly important for any organization that requires IT to remain operational (basically all of them), so it’s time to start thinking about your own strategies and how you can keep threats out of your network. One viable solution your business can implement is a Security Operations Center (SOC). What is a SOC, and […]
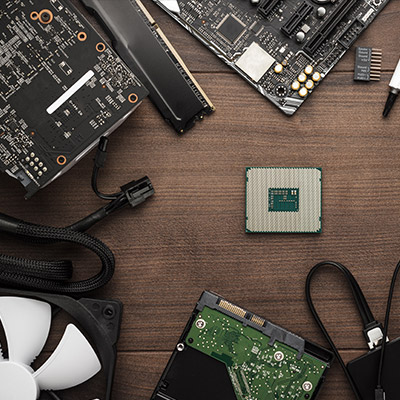
The Microprocessor Shortage Might Just Be Getting Worse

The microprocessor shortage that is affecting businesses all over the world is about to get worse before it gets better. Ukraine currently produces between 45-to-54 percent of the world’s semiconductor-grade neon, a critical component for the lasers used to make microchips. With Russia invading the sovereign nation, two of the largest neon-refinement companies, Ingas and […]
3 Strategies to Help Stretch Your Technology Budget

When you run a business you have so many variables to balance and so little time to do so that technology inevitably becomes an essential cog in your ability to manage everything. Unfortunately, technology isn’t cheap and the technology that you think you need may not be a viable purchase this year. Today, we thought […]
Focusing on Access Control Can Make Your Business More Secure

If you are someone who gets stressed out easily by people having access to resources they shouldn’t, then you probably have heard much about how to keep your data and internal resources safe from external threats. However, access control is much more than just cybersecurity; you also need to take into account the physical space […]
Social Media Conditions People to Let Their Guard Down

How often do you check social media only to find your news feed clogged with your friends and family sharing the results of quizzes like, “Which Star Wars character are you,” or “What’s your superhero name based on your birthday.” While these quizzes might seem harmless on the surface, they often hide a far more […]
How Proactive IT Management Works Better

How does your company manage its technology? Does it struggle with the idea of managing multiple workstations, server units, networking components, mobile devices, and more? If so, then read on—we have some tips to help you better manage the many different technological parts of your organization. Keep in mind that this is general advice that […]
Where IT Services Meets Physical Security

Data security isn’t the easiest thing in the world to plan for, especially if your organization doesn’t have any dedicated security professionals on-hand. While protecting your data with traditional methods, like passwords, firewalls, and antivirus, is important, what measures are you taking to make sure a thief isn’t just walking into your office and making […]
How to Get Your People on Board with Your Security Strategy

It can be tough to get your staff to care about your business’ network security, especially if they don’t consider it part of their day-to-day tasks or responsibilities. However, network security is not just isolated to your IT department; it matters to everyone, and if you can convince your staff to adhere to best practices, […]
Understanding Microsoft Services’ Price Hike

If you are a subscriber of Microsoft 365 or Office 365, you might find that your service plan will soon cost you a bit more. We just wanted to give you a warning in advance so that you’re not caught off guard, as well as to let you know we are here to help you […]
What Could a More Remote Future Potentially Look Like?

Widespread remote work is a relatively new method of operations for most businesses, but even with the limited amount of time it has been in play, the benefits it contributes have been made abundantly clear. Working on the assumption that remote work won’t be abandoned as quickly as it was adopted and instead may see […]
Hardware Shortages are Having a Major Effect on Future IT Plans
If you have tried to replace any hardware over the past couple years, chances are you were either met with significant disappointment or a hefty price tag. There is currently a hardware shortage—particularly for business electronics—and the entire business technology industry is reeling from it. If your organization depends on technology, as many do, you […]
Tip of the Week: How to Stay Focused at Work

It can be difficult to stay focused in the workplace, especially with a litany of distractions at our fingertips at just about any point in the workday. What are some strategies you can use to keep your distractions to a minimum? We’ve outlined three great tips you can utilize to stay focused on the tasks […]
Coinbase’s Super Bowl QR Snafu is Sending Shockwaves Through IT Security Circles

During the first half of the Super Bowl last month, cryptocurrency exchange company Coinbase bought a minute of ad space to broadcast an ad that was just a QR code on the screen, meandering diagonally around the screen like the famous Windows screensaver. Millions of people took out their smartphones and scanned the code and […]
How to Properly Evaluate Your Security

How effective is your cybersecurity? It seems like a simple question, but no less important to consider and determine as the answer could be the difference between a prevented breach and a successful one. In order to keep track of your business’ cybersecurity preparedness, it is important that you regularly evaluate it. Let’s go through […]
