For the remote worker, video conferencing is an essential tool. Regardless if you are a veteran of using video conferencing or if you are a new remote worker, there are some tips that can help you be a more effective member of a remote team. Let’s go through four today.
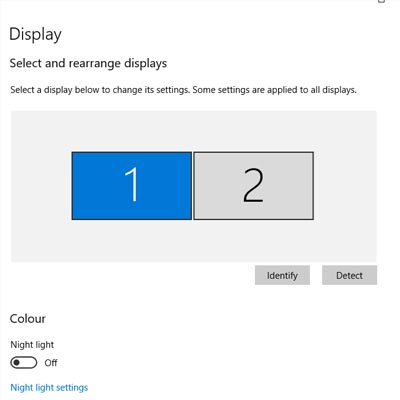
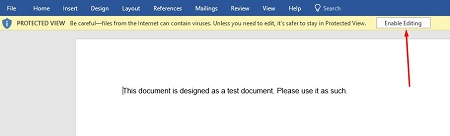
Test Your Connection and Hardware Before You Meet
Nothing is more annoying than being in a virtual meeting only to have one of your team members constantly cutting out and dropping their connection. Not only is it annoying, but it can easily cause severe miscommunications or hold up the meeting as people are asked to repeat themselves over and over again. Taking a few brief moments to test your equipment and the stability of your connection will help make your meeting significantly more productive.
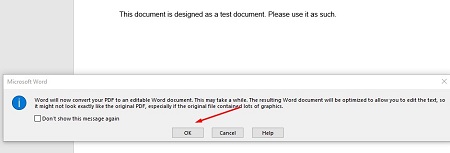
Stay on Topic
If there’s been an agenda shared for the meeting (which is something we recommend), do everything you can to stick to it. If something mentioned reminds you of something off-topic that needs to be addressed, make a note of it and follow up afterward.
The same goes if someone happens to join the meeting late. Instead of spending time circling back to bring them up to speed, make sure that someone is prepared to fill them in on what they missed afterward—if it’s something that pertains to them at all. You only have so long to meet, don’t spend that time reiterating what you’ve already covered.
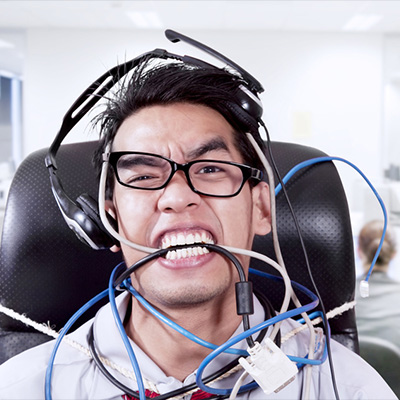
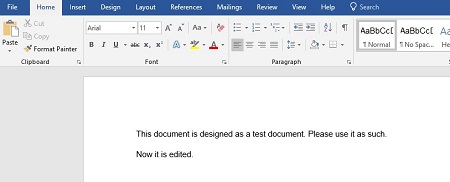
Mute Yourself Unless You’re Speaking
This one is just about being polite, but even if you’re not intentionally making any noise, a live mic can pick up more than you’d expect. Clearing your throat, sneezing, background noise…all of it can distract from the topic at hand, and most of it can be pretty gross to hear if we’re being honest. Why allow the chance of interrupting the meeting when you can eliminate it by muting yourself? Your teammates would much rather have to remind you that you’re muted than listen to the potential alternative.
That being said, you’re still on video, so try and minimize visual distractions as well. If you have a coughing fit, for instance, politely cover your mouth, or even kill your video feed until the moment has passed. Your team would much rather you vanish for a moment than watch you blow your nose, trust us.
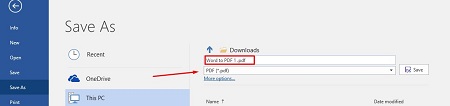
Take Notes
Whether or not someone is delegated the responsibility of taking notes during your conference, it is always a good idea to take notes for yourself, as well. This will help you keep track of whatever responsibilities were assigned to you specifically while also giving greater context to what has been discussed.
We Hope This Helps You Make the Most of Your Video Conferences
Reach out for more assistance, including a network audit to ensure that you have what you need to support successful conferencing. Give us a call at 810.230.9455 to get started!