Smartphones are firmly established as a staple of modern society. In fact, sales of smartphones grew a whopping 23 percent during the previous year. It’s the nature of mobile devices for consumers to look forward to the latest models. To that end, here’s our preview of this year’s top three smartphones.
Smartphones are firmly established as a staple of modern society. In fact, sales of smartphones grew a whopping 23 percent during the previous year. It’s the nature of mobile devices for consumers to look forward to the latest models. To that end, here’s our preview of this year’s top three smartphones.
Due to the sheer demand of smartphones flooding today’s market, there are way more than three models to choose from. However, for the sake of being concise and relevant, we’ll focus on the flagship device from these three mobile manufacturer; Samsung, Apple, and Microsoft.
Samsung Galaxy Note 5
Samsung has taken the lead as far as smartphone marketshare goes, garnering 24.6 percent of the market in 2014. They’ve achieved this success with their line of s-model phones and Note phablets. All eyes are on Samsung and its latest offering, the Galaxy Note 5.
Galaxy Note 5 Specifications
Display: 5.66-inch Super AMOLED capacitive touchscreen with 1440 x 2560 resolution made from Gorilla Glass 4
Operating System: Google Android v5.1.1 (Lollipop)
Processor: Samsung octa-core Exynos 7420
Memory: 32 GB, 64 GB, and 128 GB models available; 4 GB RAM
Cameras: 16 MP camera with optical image stabilization, 5 MP front-facing camera
Battery: 4,100 mAh
Communication: NFC, Bluetooth v4.1, Wi-Fi, Infrared, microUSB
Other features: Accelerometer, gyro, proximity, compass, barometer, gesture, UV, heart rate, Sp02, integrated s-pen
iPhone 6s
The iPhone has been Apple’s best-selling device for almost 12 years, and the iPhone 6s looks to continue this trend. The latest iPhone will include an all-new A9 processor, designed to exceed in computing power Samsung’s Exynos 7420 processor. It’s also been confirmed that the iPhone 6s will get an upgrade to its body. Presumably, this will make it stronger and more durable, especially in light of how the previous model was ridiculed for bending too easily. Additionally, the iPhone 6s will have a larger display than the iPhone 6.
iPhone 6s Specifications
Display: 4.7-inch Retina display with 750 x 1334 resolution with ion-strengthened glass and a oleophobic coating
Operating System: iOS 9
Processor: Apple A9
Memory: 32 GB, 64 GB, and 128 GB models available; 2 GB RAM
Cameras: 12 MP camera with phase detection focus, 5 MP front-facing camera
Battery: Li-Po 1,810 mAh
Communication: Bluetooth v4.1, Wi-Fi, v 2.0, reversible connector
Other features: Accelerometer, gyro, proximity, compass, barometer
Lumia 940
Microsoft recently acquired Nokia and its line of Lumia smartphones. Despite the fact that the Lumia phones have received great reviews, they’ve never made the kind of sizable impact that Microsoft would have liked. Thanks to the success of the newly-released Windows 10 OS (a system that promises one single interface across every device, including the Lumia smartphones), the time may be ripe for Windows Phone to finally take off.
Lumia 940 Specifications
Display: 5.2-inch display with 1440 x 2560 resolution with Gorilla Glass 4
Operating System: Microsoft Windows 10
Processor: Dual-core 1.82 GHz, Qualcomm MSM8992 Snapdragon 808
Memory: 32 GB, 64 GB models available; 3 GB RAM
Cameras: 20 MP camera with phase detection focus, 5 MP front-facing camera
Battery: Li-Ion 3,000 mAh
Communication: NFC, Bluetooth v4.1, Wi-Fi, microUSB 2.0
Other features: Accelerometer, gyro, proximity, compass, sensor core
These three smartphones are the flagship devices sold by each manufacture, but they’re not the only devices offered by each company. If you like what you see here, but you’re looking for variations in regards to features, check out these alternative models:
- Samsung Galaxy s6, s6 Edge, s6 Edge+
- iPhone 6+
- Lumia 940 XL
Which smartphone is right for you? While you’re sure to have personal preferences toward a particular brand, it’s in your best interest to do your due diligence when shopping for a new phone so you can obtain a model that best meets your needs. Want to know about how mobile technology like this can improve your business? Call us at 810.230.9455 to learn more.



































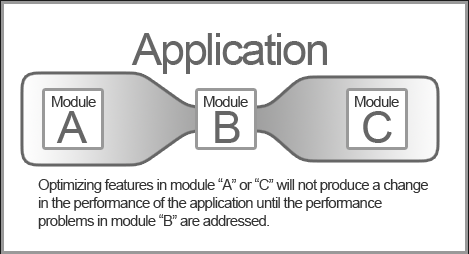 When you’re experiencing a performance-hampering bottlenecking situation with your company’s network, the challenge is to locate the source of the problem and resolve the issue so that the rest of your network can reach its full potential. This is typically done by upgrading whatever is causing the choke point so that it meets the same performance standards as other components that make up the network.
When you’re experiencing a performance-hampering bottlenecking situation with your company’s network, the challenge is to locate the source of the problem and resolve the issue so that the rest of your network can reach its full potential. This is typically done by upgrading whatever is causing the choke point so that it meets the same performance standards as other components that make up the network.