The Internet browser is one of the most utilized applications on most computers. With so many complex and aggressive issues popping up on the Internet it would be useful to know which of today’s most utilized browsers are best at keeping your computing network free from threats. Today we will take a look at each of the five most utilized web browsers to find out which is the most reliable and secure for your business to use.
What Risks Do You Face?
The risks are numerous and unrelenting. Around every corner on the Internet there are muggers with knives looking to take your stuff. The good news is that for many of the threats present, there are solutions to a lot of them–pretty much as soon as they are discovered. The Internet security community has leveraged this constant attention into immense profits. According to an article in Forbes, the cybersecurity industry is growing rapidly and is expected to be worth $170 billion by 2020, with a good portion of growth dependent on the ever-present Internet of Things.
To get a good idea about what kind of threats you face, all you need to do is take a look at the cybersecurity markets.There are cybersecurity markets for gadgets, appliances, cars, and more. There is cybersecurity insurance. PricewaterhouseCoopers has forecasted a $7.5 billion market for data insurance to come to fruition by 2020.
Four of the largest banking institutions in the world, J.P. Morgan Chase, Bank of America, Citigroup, and Wells Fargo spend upwards of $1.5 billion on cybersecurity annually. If the least risk-averse people in the world are spending a fortune, you know what you are up against. These organizations have seen companies decimated by cybersecurity lapses and understand the risk; something you and your business should consider a sign that it’s time to do something about protecting the people that depend on you against the rogue actors who breach and roam around computing networks like yours and take what they please.
Small Business Browsing
You’d think that in the context of a small business’ computing, they wouldn’t need the protection that global banking institutions do, but with all the risks that are there, there has to be some attention paid to the issue and some investment in understanding how to mitigate those risks that are laid on your organization by constant threats from the web. The good news is that most of what you need to do is attainable by simply understanding how the web works, and through the use of a secure Internet browser.
The most well-known, and most utilized, Internet browsers include: Google Chrome (56.3%), Apple’s Safari (14.5%), Mozilla Firefox (5.7%), with other browsers making up for less than 5% including Microsoft Edge/Internet Explorer, Opera and others. Any Internet browser worth its salt will do a great deal to keep users’ computers and networks from being maligned by malware and other problems.
This is accomplished by producing secure connections. In the browser, any website identified with the protocol “https://” has a secure connection. This connection encrypts the data that is sent and received through the browser to keep any transmission of data on that site from being intercepted, stolen, or leaked. This allows data to be protected during interchange providing a semblance of privacy. Since the two components every secure connection requires are privacy and identification, this encryption starts things off pretty well.
Since the typical connection between the Internet browser and any server it is cooperating with is initially short on security, websites rely on secure connections through the use of digital certificates in order to know exactly who a website is owned and run by to establish a trustworthiness of the Internet browser.
Google Chrome
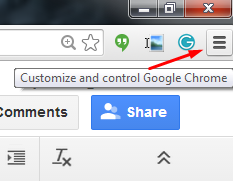
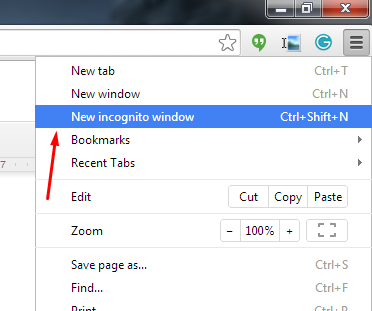
Google Chrome, long known for its reliability and popularity, sports the most powerful sandbox of any of the major browsers. A sandbox is an isolated environment that attempts to keep the Internet contained, and thus away from your network or computer. Google has the fastest response time to security vulnerabilities, but with the use of “Chrome apps”, weaknesses begin to present themselves. If you stick to the browser itself, you are looking at the most secure of the major Internet browsers.
The issue of privacy, however, makes Chrome tricky to get a hold on. Google, after all, has built an empire by knowing things about its users. This lack of privacy, even if it just results in you having more advertisements targeting you than before, is disconcerting to some and can be seen as a necessary evil for using Google’s browser.
Mozilla Firefox
Firefox is getting old. Since Firefox doesn’t utilize the sandbox technology, it doesn’t have the buffer between the user and the web that most browsers have. Firefox has a problem with their JavaScript plugins sharing the same namespace, which exposes all plugins to potential attack by any malicious plugin. In order to get the most out of Firefox, you have to understand and practice safe browsing habits, and aren’t installing plugins from developers you don’t trust.
Privacy, however has been Firefox’s strength from day one. Mozilla collects very little data and does not trade information on its users; and, remains the only of the major browsers that is open sourced. This allows users to open up the source code to see exactly what is going on.
Apple’s Safari
Apple’s browser is limited to just Apple products after attempting, and failing, to move the browser over to the PC. Safari is known for developing and releasing patches fast, and as a secure browsing experience because the risks were just not as prevalent for devices running macOS or iOS as they were for those that run Windows.
Like Chrome, and the Microsoft browsers we will mention later, user privacy isn’t on the list of priorities for Apple. While a lack of privacy could be looked upon as a positive characteristic of a browser (as more transparency helps develop bug fixes faster), if you are running a Mac OS, sticking with Safari is your best bet.
Opera
Opera is the oldest Internet browser on this list. Having gone through a major overhaul in 2013, Opera replaces their proprietary engine to go with Chromium, the same engine used by Google’s Chrome browser (and others). As far as security goes, Opera has a lot going for it. Having a small percentage of the market share is a major one (one their developers would gladly shed), as this kind of security through obscurity keeps threats to a minimum. Despite using the same browser engine as Chrome, Opera doesn’t support browser apps, limiting its already minimal exposure.
Privacy in Opera is much like Firefox’s. They have a very conservative data collection policy which despite the software not being open sourced, does present users with privacy concerns some peace of mind.
Microsoft Edge and Internet Explorer
Microsoft’s browser was once the predominant one in use. Today their market share has dwindled into the single digits, with the “new” Edge browser still gaining traction. Internet Explorer is barely being supported any longer, so it’s best to avoid that software at all costs, but Edge seems to be just a scaled down IE that doesn’t support ActiveX technology or Browser Helper Objects. It has its own limited set of in-browser apps that give people looking to infiltrate the browser more access points.
Privacy in Microsoft’s browsers is non-existent as Microsoft has a history of collecting everything. There are options to make it less transparent, but users should be happy the Edge isn’t IE.
No matter what browser you use, you have to be cognizant of sharing data you don’t want others to see. Understanding what your responsibilities are will go a long way toward keeping your data and network safe from security threats. For more information about Internet browser security and privacy, or to discuss your organization’s general network security, call NuTech Services today at 810.230.9455.