Smartphones, laptops, tablets, and other mobile technology are practically necessities in today’s modern workplace; especially if you want to keep productivity flowing at all times. However, implementing mobile devices into your workplace infrastructure is more complicated than it sounds, especially if you want to preserve security. Here are three topics to consider when implementing mobile devices in the workplace.
Data Security
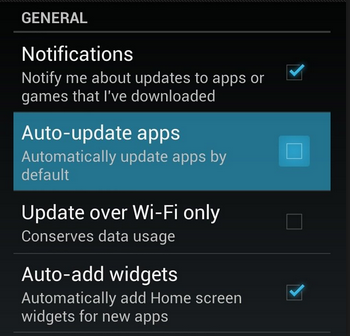
One of the key concerns that any business using mobile devices needs to account for is security. When you add new devices to your business’s network, you’re adding endpoints that could potentially fall victim to hacking attacks. The more devices that are connected to a network, the more patches and updates that need to be installed in order to maintain security. Basically, adding new devices means more work, and more work can lead to cut corners, which inevitably leads to compromised devices.
A mobile device management solution is capable of securing all of your organization’s devices, be they smartphones or laptops. It’s the easiest way to manage access to mission-critical data, whitelist and blacklist apps, and remotely wipe devices that have been compromised.
Connectivity
When you’re taking mobile devices out of the office, you need to consider how your employees (and yourself) are going to connect to sensitive corporate data. While you could just connect to your cloud solution through a public Wi-Fi connection, this is discouraged, as public Wi-Fi can often be compromised. You never know who else could be on the network, watching your every move.
In instances like these, a virtual private network (VPN) is a valuable tool. With a VPN, you can access your network’s data over an encrypted connection, meaning that as long as you are connected to a wireless network, the data sent to and from your device will be secured so that any onlookers won’t be able to do anything with your data. The data sent to your device is encrypted and then decrypted upon arrival, so if any hackers try to steal it in transit, they’ll only get a jumbled batch of letters and numbers.
Cloud Access
Of course, you’ll need access to your organization’s data, especially when you’re out of the office and using several different devices. To do so, you need a cloud solution that allows your business to share and collaborate on files in real time, across multiple platforms. Most importantly, you want to ensure that your team can open crucial data that’s needed to keep operations moving forward, even when out of the office. A dynamic cloud solution–either public, private, or hybrid–is the key to solving this pain point. Depending on your business’s specific needs, you’ll want one that prioritizes the functionality and security your business requires.
For all of your business’s mobile device security needs, you can contact NuTech Services. We’ll work with you to ensure that your devices aren’t putting your business’s data at risk. To learn more, reach out to us at 810.230.9455.



















 Monitor Your Current Data Usage
Monitor Your Current Data Usage