Passwords are the first line of defense your accounts have against the myriad of threats out there. It’s imperative that you follow industry best practices when creating them so as to maximize security. Thankfully, the latest guidelines from the National Institute of Standards and Technology, or NIST, make creating secure passwords easy.
What is the NIST?
The NIST has been the go-to authority on password creation standards for quite some time, and while they constantly change their advised practices, it is to keep up with the endlessly-shifting nature of cybersecurity. Their most recent update to password best practices can be seen in the below guidelines.
New Guidelines
Several corporations currently use the NIST guidelines and all Federal agencies are expected to adhere to them as well. Here are the latest steps in creating a secure password.
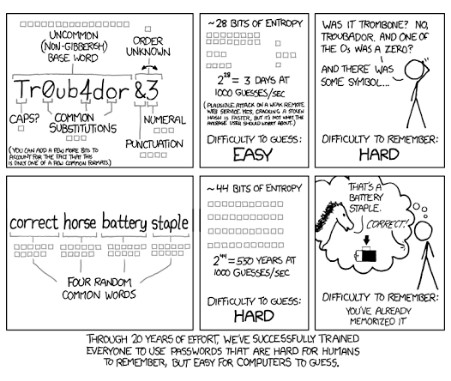
1. Length is More Important than Complexity
Password complexity has been one of the pillars of password security for years, but these days, the guidelines disagree. NIST suggests that the longer the password, the harder it is to decrypt. In fact, according to the NIST, organizations that require new passwords to be complex with numbers, symbols, upper and lower-case letters, etc, actually make the password less secure.
There are two major reasons for this determination. The first is that users often make their passwords far too complicated and forget them, leading to the eventual addition of something like an exclamation point or a 1 at the end of the password. This doesn’t make the password much more complex. Furthermore, users might be tempted to use the same complex password for multiple accounts, which is certainly not going to help their cause.
2. Eliminate Password Resets
Most businesses require that their staff reset their passwords every so often, whether it’s every month or every few months. The strategy is supposed to ensure that even compromised passwords can only be used for so long, locking would-be hackers out after the password has been changed. NIST suggests that this practice is actually counterproductive to account security.
Their reasoning is that, if people have to set passwords up too frequently, they won’t be as careful when creating them. Furthermore, when people do change their passwords, they are more likely to use the same pattern to remember them. If a previous password has been compromised, there is a good chance that this pattern can give the attacker clues into what the current password is.
3. Don’t Hurt Security by Eliminating Ease of Use
A big concern that many network administrators have is that, if they remove options such as showing a password while the user types it in or allowing copy/paste, it is more likely that the password will be compromised. The truth is that ease of use does not compromise security; it turns out that making it easier for people to properly authenticate themselves is better for security than restricting them.
4. No More Password Hints
Some systems allow for password hints where the user can assign a question and a designated answer to access the account, should they forget the password. This system in itself is flawed and the very reason why many organizations have been hacked. Thanks to social media websites and the Internet as a whole, it’s not impossible to imagine a hacker using websites or other resources to look up information on a particular user to gain access to an account. And you know what they say; once it’s on the Internet, it’s there to stay.
5. Limit Password Attempts
Placing a limit on password attempts is beneficial for your organization’s network security in just about every circumstance imaginable. Password remembrance is usually one of two things; either the user will remember the password or they will have it stored somewhere. Locking users out of their account for a short period of time can be a great way to dissuade would-be hackers from trying to guess a user’s password.
6. Use Multi-Factor Authentication
At NuTech Services, we like to reinforce with our clients that multi-factor or two-factor authentication is imperative for every account possible. The NIST recommends that users be able to demonstrate at least two of these three authentication measures before a successful login. They are the following:
- “Something you know” (like a password)
- “Something you have” (like a mobile device)
- “Something you are” (like a face or a fingerprint)
If at least two of these criteria are met, then chances are you are supposed to be on the network. Plus, consider how hard it would be for a hacker to gain access to more than one of the above. It just makes sense.
If you don’t make password security a priority for your business, you might come to regret it later, and no one wants to be the one responsible for a data breach. If you need a hand with implementing a password management system or other security best practices, reach out to us at 810.230.9455.