“What’re you in for?” a prison inmate asks. “I shared my Netflix password with my sister,” you say. This conversation might be absurd, but according to a recent ruling in accordance with the Computer Fraud and Abuse Act, it’s one that could actually happen. Now, sharing your Netflix password to let someone catch up on their favorite TV show can be considered a federal offense.
In a two-to-one ruling, three judges from the Ninth Circuit of the United States Court of Appeals declared that password sharing is a federal crime. The case in question included a former employee of Korn Ferry, David Nosal, who was headhunting his former colleagues with the intention of obtaining valid user credentials to steal data from Korn Ferry.
As expected, this landed Nosal in court, and he was charged with hacking in violation of the Computer Fraud and Abuse Act (CFAA). The CFAA has an extraordinarily wide reach, and allows the Justice Department to go after anyone who does something as meager as violating the Terms of Service agreement issued to the user of any end product (like, say, an online streaming service).
Though Nosal managed to get off the hook for his 2011 charges, he was convicted of his 2013 charges due to a ruling by a federal jury. His sentence was set for one year and one day, and earned him a felony. Yet, the one dissenting judge feels that this kind of sentence is harsh; Judge Stephen Reinhardt, who sees the larger implications of such a ruling:
“This case is about password sharing. People frequently share their passwords, notwithstanding the fact that websites and employers have policies prohibiting it. In my view, the Computer Fraud and Abuse Act (“CFAA”) does not make the millions of people who engage in this ubiquitous, useful, and generally harmless conduct into unwitting federal criminals.”
What this precedent sets is that even “generally harmless conduct,” like sharing your passwords for subscription-based streaming services like Netflix or HBO Go, can be penalized under law. Netflix only allows its service to be used in one “household,” on six different devices, with streaming capabilities on two devices at a time. The new ruling gives Netflix a reason to crack down on those who are sharing passwords without first asking them for permission to do so.
This particular interpretation of the CFAA makes it more important than ever to keep your passwords safe and secure from anyone besides yourself. After all, the more people who have access to a password, the more likely it is that the password will fall into the hands of hackers. Therefore, you should practice proper password security and keep sensitive information away from everyone who has no business accessing it.
For more trending tech news, tips, and tricks, be sure to subscribe to our blog.




























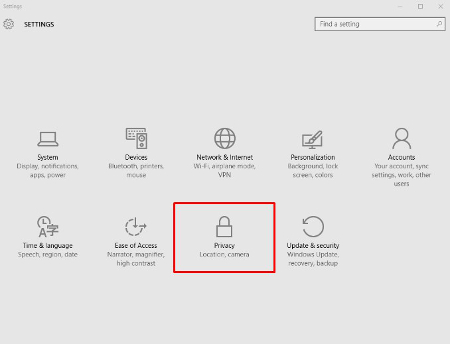
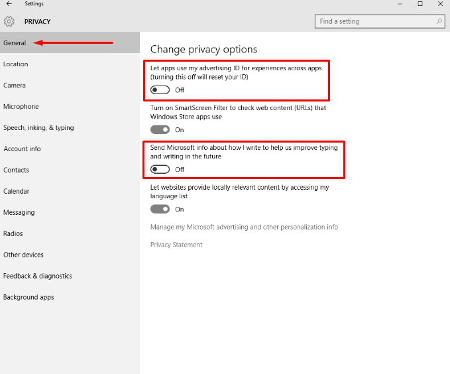 From this screen users can also turn off SmartScreen Filter if you are worried about the Windows Store syphoning links to Store items. Many users will choose to leave this option on, but will want to turn the other two off. “Send Microsoft info about how I write..” is basically a keylogger, and its practical application is to provide information for Cortana and language settings that give regional information to Microsoft.
From this screen users can also turn off SmartScreen Filter if you are worried about the Windows Store syphoning links to Store items. Many users will choose to leave this option on, but will want to turn the other two off. “Send Microsoft info about how I write..” is basically a keylogger, and its practical application is to provide information for Cortana and language settings that give regional information to Microsoft.






 Marketers Are the New Mom & Pop Store Owners
Marketers Are the New Mom & Pop Store Owners