September was National Disaster Preparedness Month, and as such, it’s important to consider the state of your business’s current backup and disaster recovery practices. Different disasters pose various threats for your organization, but many of them have one thing in common: they’re going to ruin your physical IT infrastructure, and, depending on your backup practices, could potentially bring down your entire operational infrastructure.
September was National Disaster Preparedness Month, and as such, it’s important to consider the state of your business’s current backup and disaster recovery practices. Different disasters pose various threats for your organization, but many of them have one thing in common: they’re going to ruin your physical IT infrastructure, and, depending on your backup practices, could potentially bring down your entire operational infrastructure.
Here are four of the most common natural disasters that drastically affect IT systems, and what you can do to prevent them from causing permanent damage.
Power Outages
Fierce storms are often enough to cause quite a bit of damage to businesses that haven’t taken the proper precautions. If power lines go down, you run the risk of losing electricity. This could result in your machines unexpectedly powering down, and you losing information or even causing damage to the hardware. Using an uninterrupted power supply, or UPS, can help to keep your systems up and running long enough to save any files that are being worked on. This helps to prevent damage from unexpected power-downs.
Floods and Tropical Storms
Again, storms, hurricanes, and heavy rainfall in general is enough to create problems for businesses along the coast, on bodies of water, or near rivers. Unexpected flooding is enough to cause extensive water damage, wash out foundations of buildings, and, of course, fry any technology it comes into contact with. This means that floods can potentially cost your business in not just physical repairs to your building, but also in replacing vital hardware systems.
To avoid water damage to your office’s equipment, consider placing your vital technology components in an elevated location, away from the floor. This will help keep them safe from a couple inches of water, if the flood infiltrates your building. Still, the best way to prepare for flood damage is to keep an off-site backup of your data infrastructure. This makes sure that your data isn’t wiped out by an unpredictable natural disaster.
Earthquakes
Earthquakes have the potential to be even more devastating for businesses, especially if you’re located somewhere that is known to experience periodic violent quakes. With the power to level entire buildings, your business could be at constant risk of both physical infrastructure damage and data loss.
Implementing a reliable backup and disaster recovery solution is required if you want to ensure that your data is safely stored off-site, somewhere earthquakes shouldn’t be able to reach it. You can also switch to cloud computing and virtualization tactics for your primary mode of data and application distribution, which decreases the amount of physical infrastructure networking you need to stay productive.
Fires
Just like earthquakes, a fire is one of the more damaging disasters that could hit your business. If your building were to catch fire, there’s a risk of everything you hold dear being destroyed: data, hardware, and even your physical location. Thankfully, you can at least save your data from destruction by using a backup and disaster recovery solution.
These are only a few disasters that could strike your business’s IT infrastructure. If you want to optimize your chances of making it through disasters like these unscathed, give NuTech Services a call at 810.230.9455 for more information about our backup and disaster recovery solutions.














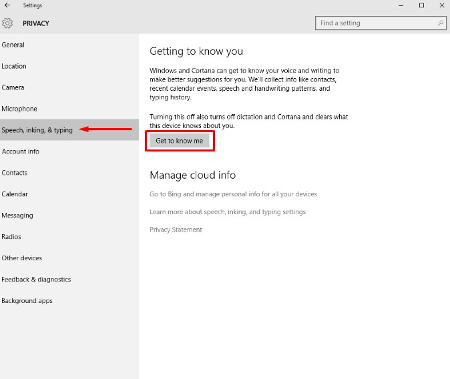
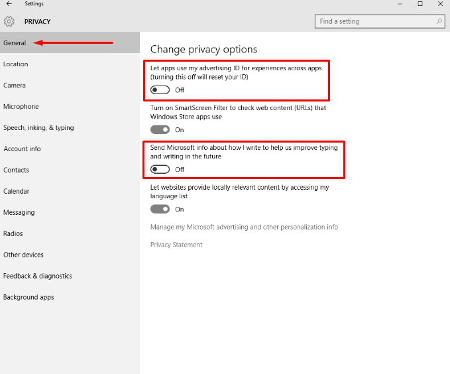 From this screen users can also turn off SmartScreen Filter if you are worried about the Windows Store syphoning links to Store items. Many users will choose to leave this option on, but will want to turn the other two off. “Send Microsoft info about how I write..” is basically a keylogger, and its practical application is to provide information for Cortana and language settings that give regional information to Microsoft.
From this screen users can also turn off SmartScreen Filter if you are worried about the Windows Store syphoning links to Store items. Many users will choose to leave this option on, but will want to turn the other two off. “Send Microsoft info about how I write..” is basically a keylogger, and its practical application is to provide information for Cortana and language settings that give regional information to Microsoft.