Many people can find it challenging to constantly remain productive, which is only understandable. Nobody can be firing on all cylinders all the time. However, this doesn’t mean that there aren’t ways that you can optimize your productivity. Here, we’ll review three general approaches to improve your productivity, with examples describing how to enact each.
1. Prioritization
One of the keys to productive work is to work smarter, not harder. By identifying what is most pressing to accomplish or otherwise needs to happen first, you can inherently increase your productivity.
Ignore Inspiration
For instance, one of the biggest causes of procrastination is taking in a project in its entirety. Seeing the entire scope of an undertaking can be intimidating, which often makes people feel as though they need to be “inspired” before they will be able to accomplish anything.
This is untrue, but can be a difficult impulse to resist. If you catch yourself falling back on this excuse, try focusing specifically on a certain aspect or piece of your greater responsibility. Once this portion is completed, you’ll most likely be motivated to continue. In essence, don’t wait to be inspired… inspire yourself through what you accomplish.
Leverage Prioritization Strategies
Another common cause of procrastination is indecision as to what aspect of a project to tackle first. Again, identifying the most important or pressing activity makes it much easier to make this decision, and there are a few ways that you can do so.
One way is to leverage something called the Eisenhower Matrix. It can be used to sort tasks based on their urgency and importance, advising you on how a task should be approached – if it should be done now, planned for, delegated to someone else, or eliminated. This tool can help you avoid spending time on activities that ultimately don’t matter as much as others, optimizing how you spend the time you have. The Pareto Principle, or the 80/20 Rule, is another means of spending your time more intelligently. By identifying the most important 20 percent of their tasks and minimizing the remaining 80 percent, many people use this principle to spend the most time on their most impactful activities.
Save Distractions for Later
We’ve all experienced that moment where, in the middle of one task, we suddenly have an idea for another. While this new task may be valuable or important, it can also hurt your operations by interrupting the one you’re engaged in at the moment… but again, this thought also needs to be addressed. Many people resolve this dilemma by creating a distraction list. Rather than suspending what they are working on, these people simply take a moment to jot down this idea for further consideration after their task is done. This means that they aren’t jumping between unfinished tasks each time a new idea pops up.
2. Preparation
Once you have your tasks organized properly, you need to ensure that you have properly made preparations to attend to them. Some of these preparations may sound counter-intuitive, but are no less crucial to your efforts.
Make Sure You’re in Order
If you aren’t ready to be productive, you aren’t going to be no matter what you try. Therefore, you need to be taking care of yourself, as well as your technology. You need to be healthy and rested to reach your potential, which means that self-care is a must. This also means that you should be strategic in how you approach your responsibilities. If you know that you tend to have a period of low energy in the late morning, it’s probably beneficial to avoid scheduling intensive tasks for that time. In addition, you need to be sure that you’re up-to-date on how things are done. The more knowledgeable you are, the more efficiently you’ll be able to make decisions, and the faster processes will move along.
Expect to Be Interrupted
The best-laid plans of mice and men often go awry, as they say. This means that you should anticipate other things to interfere with your established work schedule. What if another task pops up, or a task takes longer than anticipated? Taking these kinds of challenges into account will allow you to figure out a solution preemptively, or at least a plan that allows you to adjust and adapt.
Learn from Everything
We’ve all been taught the value of learning from our mistakes – examining situations in which things went wrong, identifying why, and avoiding those circumstances in the future. However, this is only half of what you should do to optimize your productivity. You also need to identify why your successes were successful.
Once you have completed a project or process, take some time to examine it. What about it worked well, and how could that be made better? Was every aspect necessary, or could some of it be eliminated or streamlined? Doing so will allow you to further optimize your procedure to be even more productive the next time.
3. Cheating!
In fairness, these strategies aren’t “cheating” so much as they are methods of working smarter. This way, you can make sure that your tasks are accomplished without expending more resources than they need – including your energy.
Subdivide Your Tasks
Remember the prioritization strategies we discussed above? This is a similar activity, in that you take a larger concept and divvy it up into each step that needs to be completed. Instead of putting them into a matrix or focusing on a specific set of them, the idea here is to simply make your tasks appear more achievable.
Let’s say you have to plan a work event. This alone is a significant responsibility, and can be overwhelming to approach as a whole – where to start? However, you can make your process much more comprehensible by going about it piece-by-piece, effectively expanding your task into a complete to-do list. While this does give you more tasks, they will be much easier to attain and progress with. So, instead of “Plan Party for Greg’s Retirement”, your list might include:
- Buy decorations
- Buy card
- Buy ice cream cake
- Hide cake in freezer
- Have team sign card
- Put up decorations
- Take out cake
- Send email to team to gather
More tasks, but much easier to follow nevertheless.
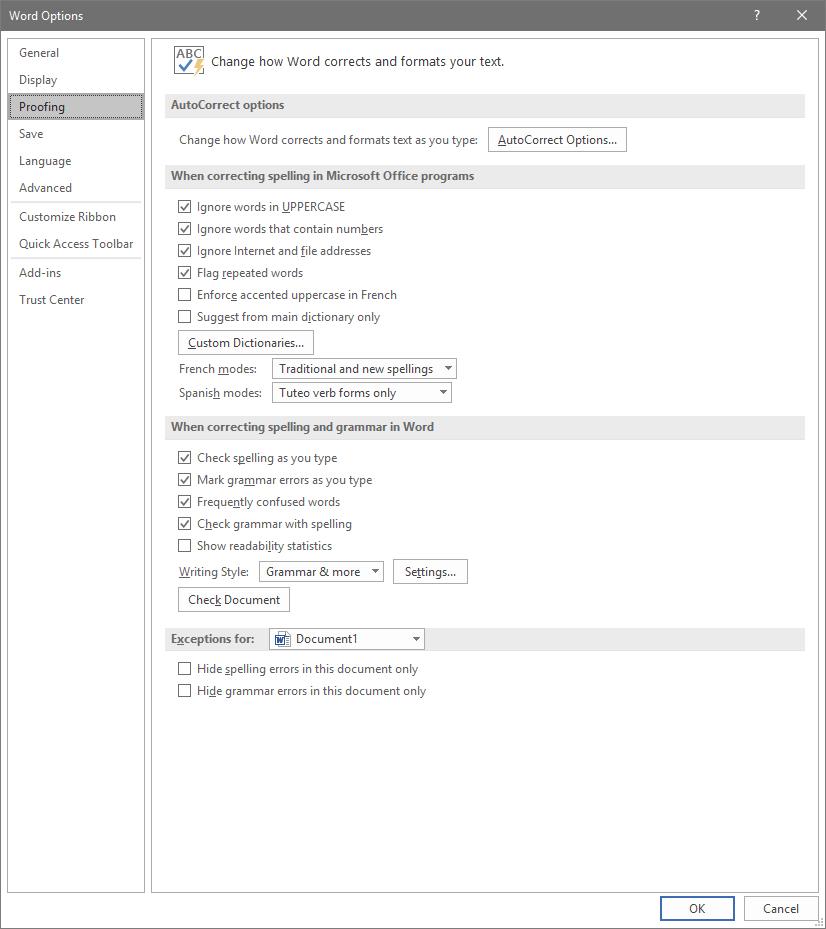
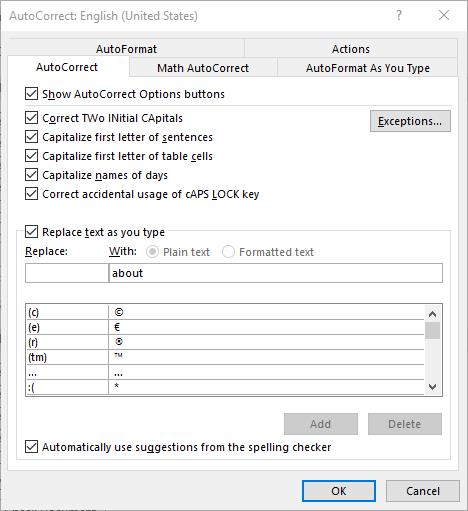
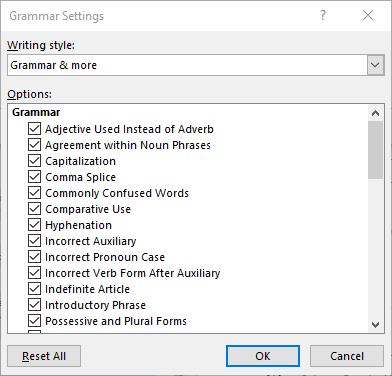
Leverage Shortcuts
There are a great many ways that your technology can offer an easier way of doing things. Naturally, keyboard shortcuts are one example of this, but so is automation. Let’s face it, any time you can save by having your technology handle something is time that you can then spend being productive elsewhere.
Eliminate Inefficiencies
How much time do you spend debating your options for truly inconsequential decisions during the day? Chances are, it’s more than you’d like to admit. The fact of the matter is that many of the choices that we are faced with aren’t all that impactful. Eliminating as many of these choices as possible will allow you to reserve your decision-making skills for the times that you really need them.
Email is another notorious source of lost productivity, simply because people don’t use it as efficiently as they could. It is too common for what should be a very brief and simple correspondence to take far longer than anticipated. Ironically, this is often because the people involved are trying to be brief.
Instead of cutting corners on your next email, invest a few minutes into including more specifics. Don’t just say you want to meet – identify the topics to be discussed. Don’t leave the time of the meeting open-ended, offer a few availabilities. While it takes longer to write, one email written this way will keep you from having to read, write, and send a few more.
Finding Your Groove
Clearly, there are many aspects to consider when you’re trying to be more productive, and some may be more effective for one person over another. A bit of experimentation will help you to land on the approach that works for you.
NuTech Services can help by providing the solutions that enable some of these methods. Reach out by calling 810.230.9455 to learn more about these solutions.