Frustrated by Your Android Device Lately? A Bad Update Might be Why

With a global market share of 71.9 percent, the Android operating system that Google provides is well and away the most utilized there is today. Despite the fact that different phone manufacturers will fiddle with the OS to fit into the devices they create, Android tends to be pretty stable—which is part of the reason […]
Should IT’s Role Be Expanding in Your Business?

Every business’ goal is to turn enough of a profit, and some businesses are better at it than others. One way that modern businesses can improve their revenue generation is by utilizing technology to cut down on inefficiencies and fuel productivity through collaboration. Today, we’ll take a look at some of the ways that businesses […]
Tip of the Week: Rearranging Your Gmail Messages

Email remains a popular tool in the business setting because of its undeniable usefulness in the office—but having said that, it can have its negative impacts on your productivity simply due to how much it can take to manage it appropriately. With so many messages that are crucial for you to keep track of coming […]
Going Over the Basics of Collaboration Solutions

With businesses depending on technology more now than ever, it stands to reason that the collaboration solutions that are available would improve as demand increases. Today’s business needs a collaboration solution that allows them to communicate, manage tasks, and be a reliable solution for teams separated by more than just a wall. Let’s take a […]
Why a Document Management System Can Be Advantageous

“Paperwork” has long been associated closely with life in the office, but like so many other “classic” workplace elements, it has been replaced by more modern means. In this case, a Document Management System (or DMS) offers a small-to-medium-sized business far more utility than its predecessor, the filing cabinet. Understanding a Document Management System Picture, […]
Tip of the Week: Politely Protect Your Data with Android Guest Mode

For many people, their mobile device contains a mixture of sensitive information and personal details. In some cases, some of the data isn’t even theirs—instead, it belongs to their workplace. Naturally, this makes many people less inclined to share the use of their device, but most people also want to avoid being rude. For precisely […]
Automation Can Bring a Your Business Serious Value
Today’s business is always searching for a leg up, and this often means doing what it can to improve their operational efficiency. Companies can approach this in several ways. They can try to cut out redundancies, they can invest in training, or for many businesses, it means leveraging innovative new technological tools that are designed […]
Building a Reliable Remote Workforce with Managed IT Services

Remote work has been a popular topic for a few years, but over the past year, with so many people forced into working from home, a lot has been written about it. Today, we wanted to briefly talk about some of the technology that is suggested for the remote business, and what we can do […]
How VoIP Can Help the Business that Adopts It

For all the communication services and tools available to businesses nowadays, the telephone remains a staple in everyday processes—despite it often being difficult to manage and expensive to maintain. This is largely because today’s technology enables businesses to use a telephone system that exceeds the capabilities once provided by telephony, for a far more manageable […]
Look How Much the Internet has Changed

When the Internet was established, it was a marvel. Now people could move information across the world in a matter of seconds. This is why the term “world wide web” was coined. Nowadays, there are literally billions of users on the Internet and the rules have had to be changed. This has some online services […]
Examining the FCC’s Efforts to Fix Internet Access in the US
Internet connectivity is an increasingly important component to a business’ capabilities in this day and age, as well as all the more crucial to an individual’s everyday life. However, with financial difficulties restricting this access for many, the Federal Communications Commission has stepped in. With a $50 subsidy being made available to low-income homes each […]
Tip of the Week: Highlighting Certain Outlook Messages

While no email platform is immune to mismanagement, Microsoft Outlook can quickly become filled with outdated and redundant messages that detract from the communication that it is meant to provide. Fortunately, there is a bit of a hack that you can use in Outlook to help prioritize your most pressing messages. Let’s dive into it. […]
How to Improve Your Business with Solid IT Practices

Technology is important to most small businesses today, especially when looking to improve it affordably. That’s why when making technology decisions, you should consider the following solid practices. Coordinate Uniform Procedures and Processes Your business should always try to find technology that works for all (or a majority) of your employees. The reason is that […]
How to Find the Right Management Software for Your Business

Software is a major part of doing business nowadays. Not only do you depend on it to manage core functions of your business, that software can be purchased in multiple different methods. When choosing management software, your business needs to choose one that fits your needs, returns long-term benefits, and provides a platform that will […]
Tip of the Week: Working with a Virtual Desktop in Windows 10

With Windows 10, you have no shortage of features and capabilities to take advantage of. One such capability: the use of a virtual desktop. Found near the Start button in your taskbar, the Task View button enables you to create and manage these virtual desktops, which we’ll discuss here. Understanding the Virtual Desktop Before we […]
What Can Be Done to Counter COVID-19-Themed Scams?
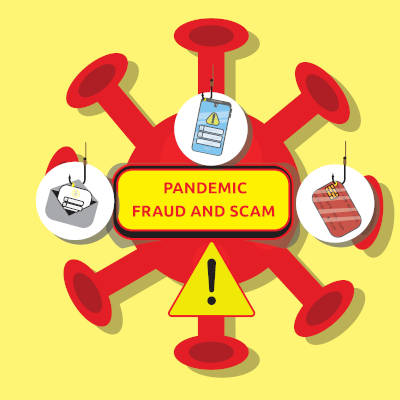
As commonly happens with any disaster, COVID-19 has inspired no short supply of scams. While these scams initially focused upon the relief funds that were delivered to people to help sustain the suffering economy, the ongoing vaccine distribution efforts have given those behind these efforts a new means of attack. Let’s consider how these scams […]
Are Utilities as Secure as They Should Be?
Recently, a story broke in Florida that sounds like something out of a terse action film: a hacker managed to access a water treatment facility and subjected the Pinellas County water supply with increased levels of sodium hydroxide. While onsite operators were able to correct the issue right away and keep the public safe from […]
Tip of the Week: Keep Track of Your Priority Gmails

Email is undeniably a useful tool, but it can be a real drag on productivity and a hindrance to manage. Then again, there are some messages that you absolutely need to keep track of as they contain sensitive information. Gmail makes keeping messages under your thumb simple. Email Can Be Frustrating Gmail offers a lot […]
Checking a Website’s Safety from Its Google Result

Google search is synonymous with searching the internet, but that hasn’t stopped them from constantly innovating the service. One of the most recent updates is to give users more context for the content that returns on search results. This works to protect users from potentially clicking on websites that could contain threats. Today, we discuss […]
Older IT Practices That Still Hold Up

While looking to the past isn’t often an idea tied to information technology, there are times when it can play a valuable role in your strategy for it. Let’s look at some modern IT concepts that rely on foundational ideas set back in the day. Securing Your Business Hardware Ensuring that your business’ hardware infrastructure […]
