There are literally billions of sports fans in the world, and the popularity of these events brings in big money; and big money typically attracts hackers. Using all types of methods, there has been a history of hacking in almost every sport. Today, we take a look at some of the most famous hacks that have shaken up the sports world.
The World Cup
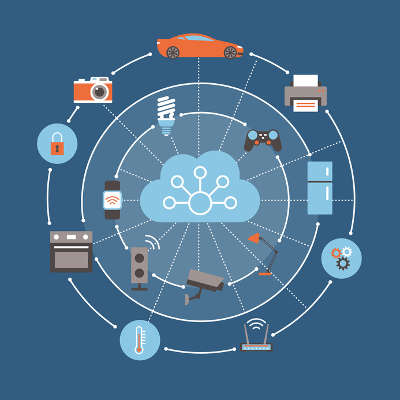
The FIFA World Cup is one of the, if not the, most popular sporting events in the world. Held once every four years, it attracts the attention of billions of people. Since the event is held every four years, it gives the host city a lot of time to get ready for possible hacker attacks. In fact, each new venue spends years and tens of millions of dollars ramping up on their cyber security.
The 2018 event held in Russia proved to be one of the most successful insofar as there wasn’t a major hack of the tournament in any way. It’s not a coincidence that typically state-sponsored Russian hackers are well known to be at the forefront of a lot of the major international sporting hacks. Fans that visited Russia from abroad during the World Cup were warned (mostly by their own governments) that they needed to be diligent not to fall into any tourist traps that would leave their cyber welfare in the hands of the thriving ecosystem of hackers that call Russia home.
Previously, in the 2014 World Cup in Brazil, the World Cup website was taken down by a distributed denial of service (DDoS) attack and thousands of visitors had their data breached through sophisticated phishing attacks. Each World Cup, especially the next one that will be held in the Middle East (Qatar) for the first time, is a goldmine for hackers.
The Olympic Games
International competitions like the Winter and Summer Olympic Games grab the eye of world for a couple of weeks. Unfortunately for athletes, coaches, and fans from all over the world, they also catch the eyes of hackers. Again, since these events are held every four years there is a long time for administrators to get ready, but that doesn’t stop those inside the host cities (or often outside of them) from trying to get over on the hundreds of thousands of people that show up to watch the events.
At the past Winter Olympics, held in Pyongyang, South Korea, the opening ceremonies were hacked by what turned out to be a Russian hacking collective. The hack caused delays in the festivities and infiltrated the games’ website, so administrators, fearing significant data loss, took down the website. Initially they had masked the attack as coming from North Korea, but it didn’t take long for professionals to ascertain that the hacks were retribution for Russia’s prohibition from the games as a result of a decade-long antidoping policy that found state-sponsored use of performance enhancing drugs; a revelation that many had suspected for decades.
While local hackers spoofed Wi-Fi and targeted athletes and guests during the 2016 Summer Olympics held in Rio De Janeiro, Brazil, Russian hackers from “Tsar Team” and “Fancy Bear” were busy hacking into the Olympic databases to gain access to athletes’ personal information. They subsequently have released some of that information, including information about gold medal gymnast Simone Biles, and tennis legend Venus Williams.
NFL
In the United States, it doesn’t get much bigger than the National Football League. In fact, one study showed that about one-third of all church-going males don’t go to church from Labor Day to New Years. Nearly 30 million people tune in to watch the NFL each Sunday. With this popularity comes attention; and hackers have used this popularity to their advantage.
In 2016 NFL commissioner Roger Goodell’s Twitter feed was hacked with a message that announced that he had passed away. The perpetrator happened to be a teenager from Singapore. In February 2017, 1,135 NFL players had their personal information stolen by hackers when the NFL’s union, the NFLPA, was hacked. Hackers made off with 1,262 people’s personal information, their financial data, their home phone numbers, their addresses and more.
In 2009, a man named Frank Tanori Gonzalez was given an extremely lenient sentence for hacking into the standard-definition communications feed at Super Bowl XLIII with a clip from an adult film that aired unedited throughout the greater Tucson area (the game was held in Tampa, FL).
MLB
Major League Baseball makes over $10 billion a year, and they do a phenomenal job of protecting their brand online. MLB makes a lot of their money in media and has made it a point to prioritize cyber security for league business. With individual teams handling their own cyber security, there have been small hacking cases, but unlike most other sports the biggest hacking scandal in baseball history was carried out by a team executive.
From 2013 to 2014, St. Louis Cardinals’ former scouting director, Chris Correa, repeatedly accessed the internal communications server of former division foe Houston Astros. The Astros had moved to the American League from the National League after the 2012 season, and they had hired former statistician Sig Mejdal from the Cardinals. When Mejdal left St. Louis he turned in his laptop. Using the information he got off this laptop, Correa figured out Mejdal’s new password and started entering the Astros network. For his indiscretions Correa got 46 months in federal prison.
NBA
The most famous hack in NBA history is hack-a-Shaq, which was a strategy used to limit Shaquille O’Neal’s effectiveness by making him shoot free throws (with which he struggled mightily), but there have been a few other hacks that have affected NBA players. The most notable, was NBA player Ty Lawson having his computer hacked and held his personal data for ransom in 2016.
Another situation was what is called a catfishing scam that involved NBA forward Chris Andersen and model Paris Dylan. A woman named Shelly Chartier had used multiple people’s online messaging accounts to manipulate Anderson and Dylan into bad situations. Andersen ended up being raided by the Douglas County sheriff’s department because Dylan was 17 at the time and any digital possession of lewd material would be legally considered child pornography. After investigators uncovered the scheme, Chartier was arrested and sentenced to 18 months in prison. Anderson continued his NBA career and Dylan was able to put the situation behind her and is now is an Internet model.
PGA
Recently, the PGA of America held the 100th PGA Championship at Bellerive Country Club just outside of St. Louis, Missouri. As the golfers were navigating their first rounds, the PGA was under attack by hackers. A message was sent to administrators that read, “Your network has been penetrated. All files on each host in the network have been encrypted with a strong algorthym[sic].” The hackers also sent a Bitcoin wallet number with instructions on how to deposit money.
The PGA of America immediately hired a third-party IT security firm to solve the problem. Since security professionals from all over the world consider these extortion attempts to be futile against the diligence and expertise of security professionals, the line is usually to not pay and hope that the data can be recovered without the encryption key. Only time will tell how the situation is resolved.
Other sports leagues and athletes have had to deal with major problems from hackers over the years, including the English national rugby team’s website being hacked by the Islamic State in Syria (ISIS), and four-time Tour De France champion Chris Froome’s performance data was hacked as a rival team was convinced he was using performance enhancing drugs.
There are dozens of ways that you can fall victim to hackers. If your business isn’t already doing all it can to protect your digital assets, the time is now. Reach out to the IT professionals at NuTech Services for more information on the best way to protect your business from outside (and inside) threats at 810.230.9455.