Let’s say that you are a consumer looking to take advantage of data backup in an affordable way. You want a way to keep your data safe in the event of a disaster. For the average PC user, Google Drive now allows users to take backups of specific files and folders via the Backup and Sync application on their desktop PC.
Keep in mind that we are only discussing the possibility of Google Drive as an adequate backup solution for the average PC user. For businesses that want to ensure minimal downtime and maximum data recovery, your best chance is to implement an enterprise-level backup and disaster recovery solution. If you want a powerful backup solution, be sure to reach out to us and ask about your options.
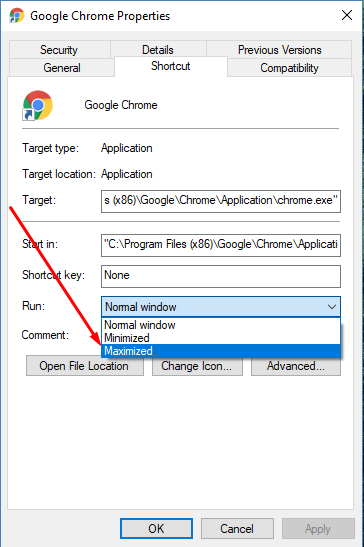
In essence, Backup and Sync is the latest version of Google Drive, and allows users to back up specific files or folders on their desktop PC, and send them to Google Drive. This is particularly great for consumers who want to keep backups of their photos, videos, and other media. Google understands that this feature is primarily meant for consumer use, and encourages their G-Suite customers to wait patiently until their Drive File Stream feature is available.
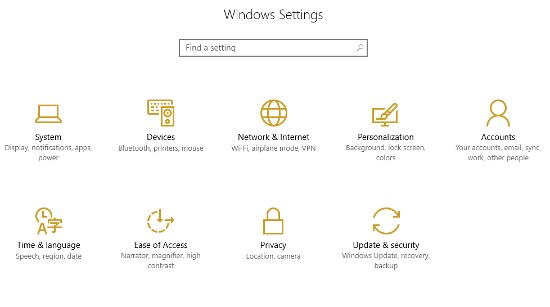
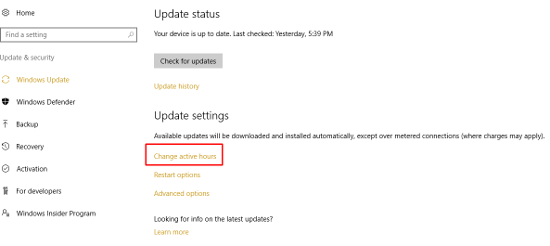
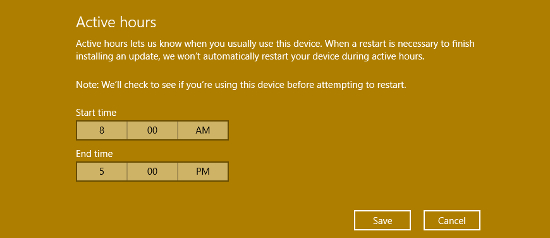
In terms of availability, Backup and Sync can be implemented by users using Google Drive for PC, as well as for Mac. Just keep in mind that using Backup and Sync to store your videos and photos will likely result in your exceeding the free Drive space offered by Google.
One thing to think about as a business owner though; you shouldn’t let employees store company data directly on their workstations. Files should be stored centrally on the server where you back it up. If your workstations have a lot of sensitive company data on them, a disgruntled employee could easily set up Google Drive Backup to grab and steal all of your data. It doesn’t hurt to be a little paranoid over your data and where it’s stored.
As always, you can count on NuTech Services to inform you about the latest and greatest business technology solutions for your organization’s needs. If you need help with managing data backup and recovery, you’ll find no one better suited to the task than us. To learn more about your business’s data backup options, reach out to us at 810.230.9455.