
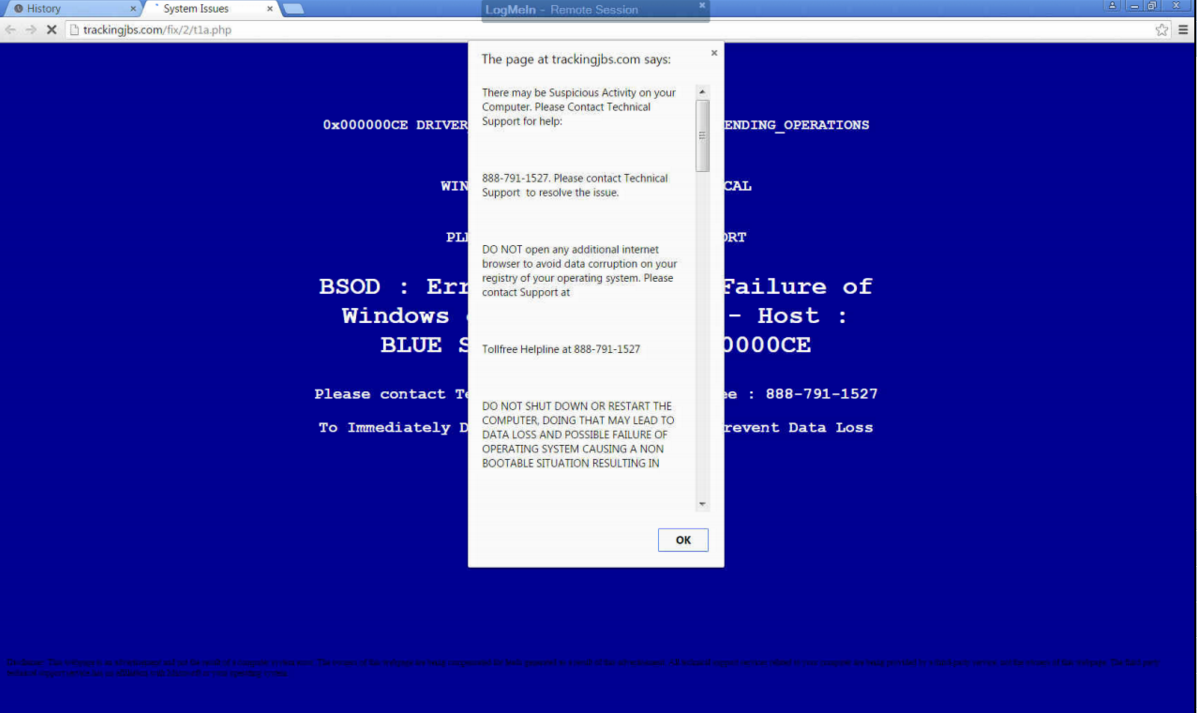
The ransomware Petya (previously thought to have been eradicated) has unfortunately resurfaced, and it’s brought a friend to the party. Petya was delivered via an email containing an invitation to apply for a job, including the virus in an executable file that was disguised as a PDF job resume. When a hepless user clicked the file, Petya would get to work.
The original version of the ransomware operated by restricting access to the master boot record, allowing access only to a dark web payment portal that may (or may not) fix the problem. Since Petya required administrative privileges to do so, a savvy user could render it useless by denying them. Unfortunately, its developers have come up with an unpleasant way to work around this Achilles heel.
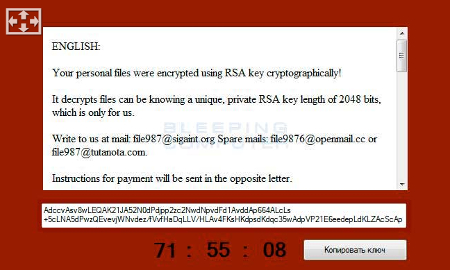
The malware now comes bundled together with a second ransomware program, a more traditionally operating one known as Mischa. Mischa blocks access to files until the user pays a ransom, providing the user with links to TOR payment sites and authentication codes to utilize there as well. The kicker is, Mischa also encrypts executable files, leaving the Windows folder and browser folders untouched. Once the computer has been sufficiently infected, Mischa leaves two files for the user with their payment instructions.
Just as when Petya was originally distributed, an email is delivered containing a file appearing to be a job application, which would ask to run an .exe file. Selecting “yes” will download Petya, and selecting “no” used to foil the attack. Not anymore – now selecting “no” will install Mischa.
The payment site for Mischa works in a very similar manner to Petya’s. After inputting the authentication code, the user is ordered to purchase enough Bitcoins to pay the ransom, currently set to the general equivalence of $875. The user is then provided with the Bitcoin address where they are to send the ransom.
Unlike Petya, there is no known way to recover files affected by Mischa without paying the Bitcoin ransom, but there are tools available online to remove the virus.
However, also to be found online are the rumblings of upcoming copycats of Petya and Mischa. Malwarebytes.com posted a threat analysis of another dual-horned ransomware called Satana. Just like the Petya and Mischa bundle, Satana has the capability to lock the master boot record and the complete file record. The main difference is, while Petya and Mischa would only run one of the two malware options depending on the user’s actions, Satana goes right ahead and runs both, sequentially.
While Malwarebytes reports that Satana is currently flawed and appears to still be in the early stages of development, this news is still unsettling. Imagine how frustrating it would be to have no fighting chance after downloading a virus – and now consider that we could be approaching that point.
However, we will continue to monitor the situation and keep you in the loop with any updates that arise. Keep visiting the NuTech Services blog to check in for the latest news and security updates.













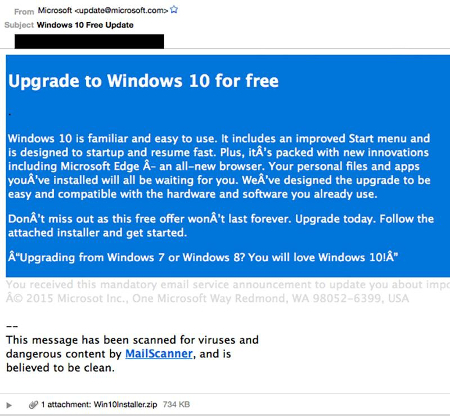


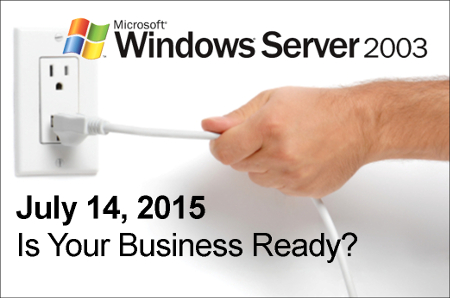 It’s best practice to upgrade your server’s OS (and all of your software for that matter) every time a new version is released–not every twelve years. One reason to upgrade is that the latest software is built to handle the demands of modern businesses, which gives you a competitive edge over companies running older software. Security is another big part of why you should upgrade, and in the case of Windows Server 2003, the need to upgrade by July 14th is urgent because Microsoft ending mainstream support means that they will no longer be providing security updates and patches to protect you from the latest threats.
It’s best practice to upgrade your server’s OS (and all of your software for that matter) every time a new version is released–not every twelve years. One reason to upgrade is that the latest software is built to handle the demands of modern businesses, which gives you a competitive edge over companies running older software. Security is another big part of why you should upgrade, and in the case of Windows Server 2003, the need to upgrade by July 14th is urgent because Microsoft ending mainstream support means that they will no longer be providing security updates and patches to protect you from the latest threats.